01 // The Challenge
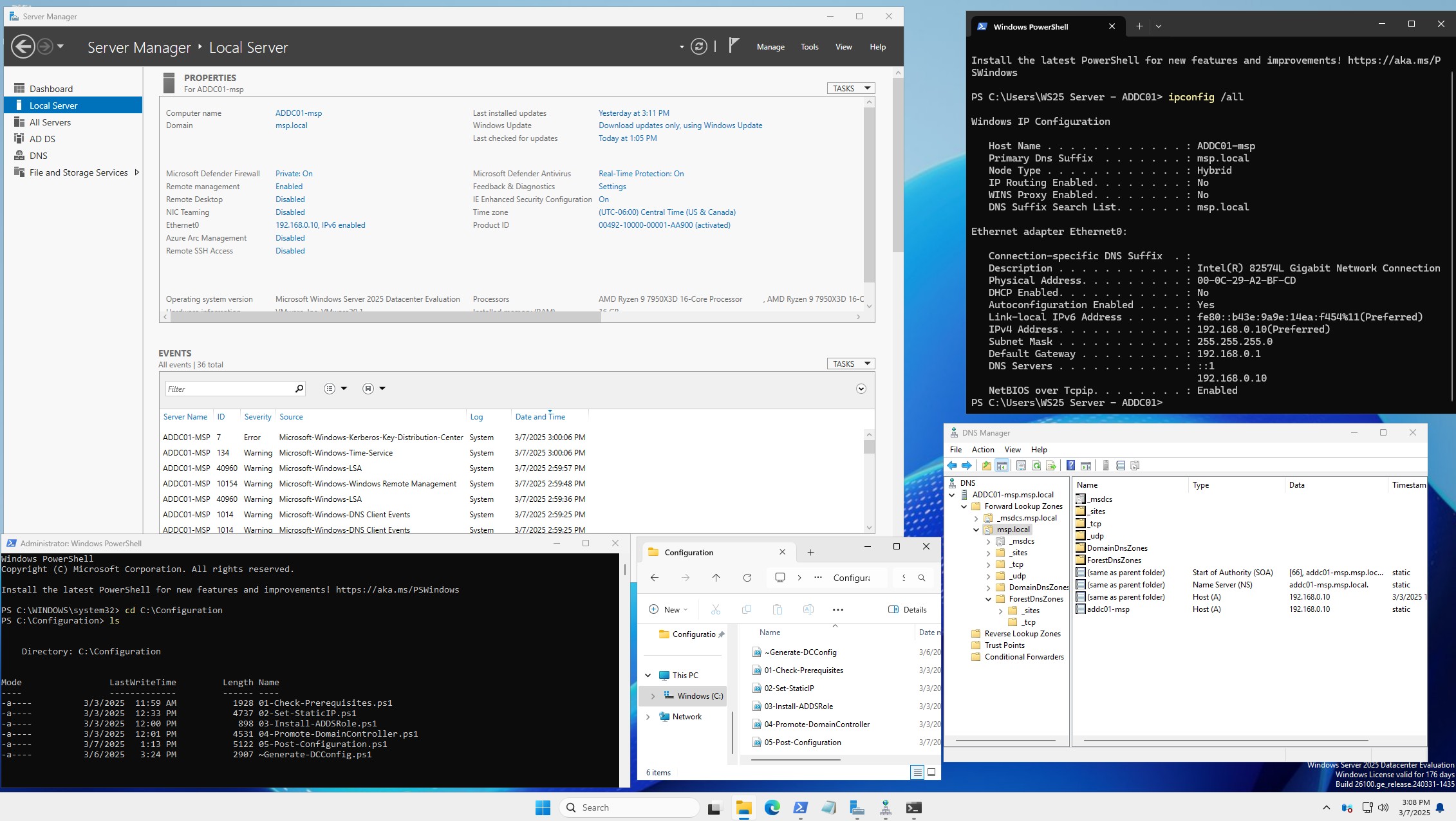
MSP techs stand up new Active Directory environments constantly — for new tenants, for lab rebuilds, for failovers. Done by hand in Server Manager it's a slow, checklist-driven, error-prone process: promote the server, install ADDS, configure DNS, set the domain functional level, create the first OUs and groups, configure the password policy, join admin machines, and so on. Every step is a chance to forget something.
02 // The Script
- Role install —
Install-WindowsFeature AD-Domain-Services -IncludeManagementTools. - Forest creation —
Install-ADDSForestwith parameterized domain name, DSRM password, and functional level. - DNS — configured alongside AD, with forwarders set to client-approved upstream resolvers.
- OU structure — idempotent
New-ADOrganizationalUnitcalls for Users, Computers, Service Accounts, and Admins. - Groups & accounts — role-based security groups seeded with default delegation for helpdesk and senior techs.
- Password policy — fine-grained PSOs applied to privileged groups.
- Logging — every action transcripted to a timestamped log file for post-deployment audit.
03 // Design Choices
Idempotent. Running the script twice on the same server is safe — each step checks for existing resources before creating them. This matters because real deployments get interrupted (reboots, timeouts, RDP drops) and the tech needs to resume without worrying about duplicates.
Parameterized. Domain name, admin password, OU layout, and forwarders are all inputs. The same script deploys to any tenant — the tech just fills in the parameters.
Auditable. Full PowerShell transcripts plus a structured JSON summary of what was created, for compliance review or troubleshooting later.
04 // Results
05 // Next Steps
Wrap the script in a small deployment UI (WPF or web) so non-PowerShell techs can fill the parameters through a form, and add a GPO-import step to seed baseline group policies from a signed template.
Where this went next. This single-server script was the seed for a much larger project — a full two-site Active Directory forest (two domain controllers, DNS, DHCP, a certificate authority, and Windows + Linux clients) provisioned from bare install media with Ansible on KVM, then tested with live disaster-recovery drills. Read it here: Building a Two-Site Active Directory From Code.
Source is open at github.com/marky224/Active-Directory-Domain-Controller-Provisioning.